I will give a presentation on “Perception of the Public on Security Technology” at the academic workshop ‘Socially Responsible Innovation in Security’ organized by University Centre Saint-Ignatius Antwerp on 22 October 2015.
Schlagwort: Security

Workshop: Privacy @ PACITA conference
The FP7 projects PRISMS and SurPRISE are organizing a workshop on “Security and Privacy Perceptions of European Citizens: Beyond the Trade-off Model” at the 2nd European Technology Assessment Conference in Berlin (26 February 2015)

Privacy is important to European citizens – but there are large differences between the countries
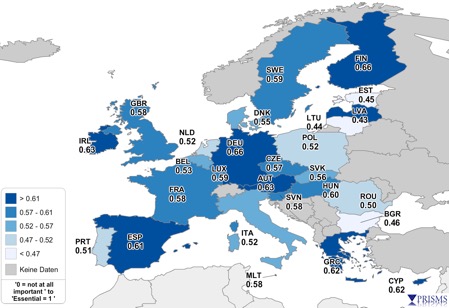
New research has found that on average 67 % of European citizens think that the protection of their privacy is important or very important.
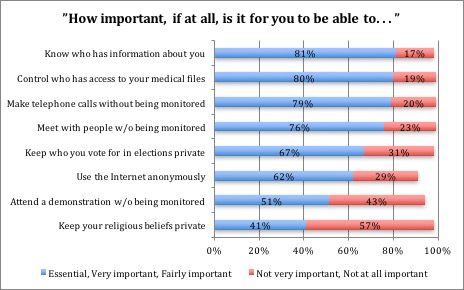
The research, conducted by the EU funded PRISMS project, surveyed (between February and May 2014) more than 27,000 European citizens over the age of 16 and found that citizen think find it especially important „to know who has information about them“, to have „control who has access to their medical files (both 80%), to „make telephone calls without being monitored“ (79 %) and to „meet people without being monitored“ (76 %).
The survey showed, however, that there are significant differences throughout Europe. Measured on a scale from 0 (not at all important) to 1 (essential) the overall importance of privacy for citizens ranges from 0,46 in Bulgaria to 0,66 in Germany and Finland.
The researchers found that the citizens’ assessment is often related to their trust in institutions such as government bodies but also businesses. Countries with a particular high trust include Finland, Germany while trust in institutions is low in Bulgaria and Portugal. There are, however, a few countries with authoritarian historical experiences (Spain, Greece) where citizens considered privacy important and have little trust in government bodies in particular.

Europeans want security and privacy – and, oh yeah, privacy is not dead
Privacy is not dead, as the results of a major telephone survey of more than 27,000 respondents across Europe has found: 87% felt that protecting their privacy was important or very important to them. Even more, 92%, said that defending civil liberties and human rights was also important or very important.
The survey may be the most detailed assessment of how people in 27 EU Member States feel about privacy and security. It was conducted as part of the EU-funded PRISMS project (not to be confused with the once-clandestine PRISM program under which the US National Security Agency was collecting Internet communications of foreign nationals from Facebook, Google, Microsoft, Yahoo and other US Internet companies).
The survey showed that privacy and security both are important to people. There were some consistent themes, e.g., Italy, Malta and Romania tend to be more in favour of security actions, while Germany, Austria, Finland and Greece were less so. Respondents were generally more accepting of security situations involving the police than the NSA.
60% said governments should not monitor the communications of people living in other countries, while one in four (26%) said governments should monitor such communications, while the remainder had no preference or didn’t know. Predictably, there were significant differences between countries. Three out of four respondents in Austria, Germany and Greece said governments should not monitor people’s communications, which was somewhat higher than most other EU countries.
70% of respondents said they did not like receiving tailored adverts and offers based on their previous online behaviour. 91% said their consent should be required before information about their online behaviour is disclosed to other companies. 78% said they should be able to do what they want on the Internet without companies monitoring their online behaviour. 68% were worried that companies are regularly watching what they do.
Some other results: 79% of respondents said it was important or essential that they be able to make telephone calls without being monitored. 76% said it was important or essential that they be able to meet people without being monitored. More than half (51%) felt they should be able to attend a demonstration without being monitored.
80% said camera surveillance had a positive impact on people’s security; 10 % felt it made no difference and even fewer (9%) felt it had a negative impact. Almost three-quarters (73%) said the use of body scanners in airports had a positive impact on security, while fewer than one in five (19%) felt that the use of scanners had a negative impact on privacy. 38% said smart meters threatened people’s rights and freedoms.
More than one in five (23%) said they had felt “uncomfortable” because they felt their privacy was invaded when they were online. Almost the same (21%) felt uncomfortable because they felt their privacy was invaded when a picture of them was posted online without their knowing it. By contrast, a substantial majority (65%) didn’t feel uncomfortable when they were stopped for a security check at an airport. Respondents were asked if they had ever refused to give information because they thought it was not needed. 67% said yes, while 31% said no. Half of all respondents said they had asked a company not to disclose data about them to other companies.
While the survey generally showed that people were concerned about their privacy, there were some surprises. For example, 57% said it was not important to keep private their religious beliefs. Almost one-third (31%) said it was not important to keep private who they vote for. Only 13% had ever asked to see what personal information an organisation had about them. More than half (51%) had not read websites’ privacy policies.
Respondents had a very nuanced view of surveillance and its impact on their privacy. Support or opposition to surveillance depends on the technology and the circumstances in which it is employed, if for example the surveillance activity was targeted and independently overseen.
The interviewers gave respondents eight vignettes, or mini-scenarios, and then asked them for their views on the privacy and security impacts, some of which are highlighted below. The vignettes concerned crowd surveillance at football matches, automated number plate recognition (ANPR), monitoring the Internet, crowd surveillance, DNA databases, biometric access control systems, NSA surveillance and Internet service providers’ collection of personal data.
A sizeable minority (30%) felt that monitoring demonstrations threatened people’s rights and freedoms, but that figure fell to 19% if the monitoring was of football matches. 70% felt crowds at football matches should be surveilled; 61% said surveillance at football matches helped to protect people’s rights and freedoms.
Opinion was more evenly divided about DNA databases: 47% felt that DNA databases were okay compared to 43% who did not agree. However, a substantial majority, 60%, opposed NSA surveillance and 57% felt NSA surveillance threatened people’s rights and freedoms.
Also predictably, there were differences in political views. 68% of people on the left felt that foreign governments’ monitoring people’s communications was a threat to their rights and freedoms, compared to 53% of people on the right who felt this way. 60% said these practices made them feel vulnerable. More than half (53%) did not feel these practices made the world a safer place. 70% did not trust government monitoring of the Internet and digital communications. In response to a question about how much trust they had on a scale of 0 (none) to 10 (complete) in various institutions, more than half (51%) of all respondents said they had little or no trust in their country’s government compared to 39% in the press and broadcasting media and 31% in the legal system. Half of all respondents had some or complete trust in businesses, and an astounding 70% trusted the police.
Interviewers described a scenario in which parents find out that their son is doing some research on extremism and visits online forums containing terrorist propaganda. They ask him to stop because they are afraid that the police or counter-terrorism agencies will start to watch him. 68% said security agencies should be watching this kind of Internet use, compared to 20% who said they should not. 53% said security agencies’ doing this helps to protect people’s rights and freedoms. One in five (22%) disagreed. 41% of respondents felt that parents should worry if they find their child visiting such websites. One in five felt parents should not worry because they believed that security agencies can tell the difference between innocent users and those they need to watch.
Another vignette concerned companies wanting to sell information about their customers’ Internet use to advertisers. The companies say the information they sell will be anonymous, but 82% of respondents still said service providers should not be able to sell information about their customers in this way. The figure was 90% in Germany and France, the highest in Europe. 72% of respondents in the UK and across the Union felt such practices were a threat to their rights and freedoms.
The European PRISMS project started in February 2012 and finished in August 2015. The project has been analysing the traditional trade-off model between privacy and security and devising a more evidence-based perspective for reconciling privacy and security. Among other things, the project is examining how technologies aimed at enhancing security are subjecting citizens to an increasing amount of surveillance and, in many cases, causing infringements of privacy and fundamental rights. The project is also devising a decision support system aimed at those who deploy and operate security systems so that they take better account of how Europeans view privacy and security.
The project has been undertaken by a consortium comprising eight partners from five countries: the Fraunhofer Institute for Systems and Innovation Research (Germany), TNO, the Dutch research organisation, Zuyd University (Netherlands), the Free University of Brussels, the Eötvös Károly Policy Institute (EKINT) in Hungary and three partners from the UK: Trilateral Research, Ipsos MORI and Edinburgh University.
Ipsos MORI conducted the interviews between February and June last year, since when the other partners have been poring over the results and are now making some of the survey results and their analysis publicly available. The PRISMS consortium said further analysis of the survey data would examine the relationships between demographics, attitudes and values in relation to privacy and security.
More results from the PRISMS project can be found at prisms-project.eu.
David Wright and David Barnard-Wills

Schüren Vertrauensprobleme die Angst vor Massenüberwachung in Europa?
David Barnard-Wills argumentiert, dass EU-Bürger für ihre Sicherheit nicht unbedingt mehr von ihrer Privatsphäre aufgeben wollen – und dass Politiker dies bei Entscheidungen über Überwachungspraktiken Ernst nehmen sollten.
Angeheizt durch Edward Snowdens Enthüllung von immer mehr Details der Überwachungspraktiken von NSA und GCHQ, hat es in den vergangenen Monaten eine intensive Berichterstattung der Medien über Motive und Grenzen der staatlichen Überwachung gegeben und wie die Bürger über das Verhältnis von Sicherheit und Privatheit denken. Dies hat auf nationaler wie auch europäischer Ebene erhebliche politischer Aufmerksamkeit erregt. Bürgerrechtsgruppen haben Protestaktionen gegen Massenüberwachung organisiert, zuletzt am 11.2. unter dem Motto „The day we fight back“ (Der Tag, an dem wir zurückschlagen).
Es ist daher sowohl für Sozialwissenschaftler und Politiker besonders wichtig und drängend, die Reaktionen der Bürger auf die zunehmende Überwachung genauer zu verstehen. Welche Faktoren sind besonders kritisch und führen zu öffentlichen Protesten und unter welchen Umständen ist die Öffentlichkeit bereit, bestimmte Überwachungs-und Sicherheitsmaßnahmen zu akzeptieren?
Das von der Europäischen Union finanzierte Projekt PRISMS (Privacy and Security Mirrors) versucht, genau dies zu untersuchen. Es versucht, das Verhältnis zwischen Privatsphäre und Sicherheit zu analysieren und eine evidenzbasierte Perspektive für die Vereinbarkeit von Privatsphäre, Sicherheit und Vertrauen zu entwickeln. Es wird untersucht, wie sogenannte Sicherheitstechnologien Bürger zunehmend überwachen und dabei in vielen Fällen die Privatsphäre und andere Grundrechte verletzen.
Eines der wichtigsten Ziele des Projektes ist es, die sehr vereinfachte Annahme zu überwinden, wonach die Bürger Privatheit und Sicherheit als Nullsummenspiel betrachten und es akzeptieren, für ein Mehr an Sicherheit in zunehmendem Masse ihre Privatheit und informationelle Selbstbestimmung aufgeben zu müssen. Als Ergebnis soll das Projekt solche Faktoren ermitteln, die die Einstellungen der Bürger zu Privatheit und Sicherheit beeinflussen und in die Bewertung spezifischer Sicherheitstechnologie einfliessen. Die Berücksichtigung solcher Faktoren in Politik, Verwaltung und Unternehmen kann zu besseren Entscheidungen über Überwachungspraktiken beitragen.
Das Projekt lässt seit Mitte Februar vom Meinungsforschungsinstitut Ipsos Mori eine Befragung von 27.000 europäischen Bürgern durchführen, um ein genaues Bild über deren Einstellung zu Privatsphäre und Sicherheit zu erstellen, also zu einer Zeit, da diesen Themen eine erhöhte öffentliche Aufmerksamkeit erhalten. Erste Ergebnisse der Befragung werden im April 2014 verfügbar sein, aber bereits zur Vorbereitung der Umfrage wurden Fokus-Gruppen mit Bürgern in Deutschland, Belgien, Portugal, Dänemark, Estland, Ungarn, Rumänien und Großbritannien durchgeführt.
In den Fokusgruppen hatten viele der Teilnehmer das Gefühl, dass ihre Privatsphäre schwer zu schützen ist, wenn sie an der modernen Gesellschaft teilhaben wollten. Dennoch war ihnen zumindest prinzipiell der Schutz ihrer Privatsphäre und ihrer persönlichen Daten sehr wichtig.
In den meisten Ländern waren die Teilnehmer der Ansicht, dass sie selbst die Hauptverantwortung für den Schutz ihrer Privatsphäre hätten. Allerdings erwarten Sie auch von den Regierungen ihrer Länder ersthafte Bemühungen, die richtigen Rahmenbedingungen zum Schutz ihrer Rechte zu entwickeln. Schließlich wünschen sie sich auch eine wirksame Durchsetzung dieser Rechte durch staatliche Stellen wie die Polizei und Aufsichtsbehörden. Organisationen, die personenbezogene Daten erheben, sollten dafür verantwortlich sein, dass diese sicher und rechtskonform gespeichert und verarbeitet werden.
Die Teilnehmer der Fokusgruppen wünschten sich in der Regel robuste Anwendungsfälle für Überwachungstechnologien, die auch umfänglich die Interessen der Betroffenen berücksichtigen. Insbesondere wollten die Personen würdevoll und individuell behandelt werden, ohne von Vorherein unter Generalverdacht zu stehen. Bei der Einführung von Technologien, von denen ihre Rechte unmittelbar berührt werden, wünschen sie sich eine frühzeitige und ernsthafte Information über die Funktionsweise und Implikationen der fraglichen Technologie und eine ernsthafte Konsultation der Bürger.
Der konkrete Kontext war allen beteiligten Bürgern sehr wichtig, zum Beispiel war die Akzeptanz von Sicherheits- und Überwachungstechnik auf Flughäfen höher als bei Anwendungen in anderen Lebensbereichen, wie z.B. von intelligenten Stromzählern. Die Vorteile solcher Smart Meter für die Verbraucher waren vielen Bürgern wenig einleuchtend.
Bei der Internetnutzung nehmen Bürger mittlerweile vielfach an, dass ihr Verhalten von staatlichen Stellen breit überwacht werden, um Terrorismus und organisierter Kriminalität vorzubeugen und halten dies (mit der Ausnahme der Deutschen) auch für legitim.
Bürger haben bei Überwachungspraktiken von Unternehmen noch größere Bedenken als bei (rechtmäßiger) staatlicher Überwachung. Sie hatten dabei vor allem Sorgen über die Folgen solcher Praktiken auf ihre körperliche und finanzielle Sicherheit. Die Bürger äußerten das Gefühl, dass sie mit der Wahrung ihrer Rechte sowie moralischen und kulturellen Werte gegenüber Unternehmen in vielen Fällen überfordert sind und hier vor allem der Staat in der Pflicht sei, die notwendige Balance zwischen den Interessen herzustellen.
Diese Befunde haben Konsequenzen für die Governance der Überwachung in Europa. Datenschutz und Privatsphäre sind immer noch wichtige gesellschaftliche Werte und sollten geschützt werden, auch wenn die Teilnehmer sagen, dass es in Einzelfällen, wie zum Beispiel Flugreisen, eingeschränkt werden könnte. Momentan seien die überzogenen staatlichen Sicherheitsansprüchen (Sicherheit als „Supergrundrecht“) nicht in Übereinstimmung mit den individuellen Bedürfnisse nach Sicherheit und Privatheit.
Die PRISMS Forscher der Freien Universität in Brüssel (VUB) haben vorgeschlagen, dass die Art und Weise, wie die Angst vor der Kriminalität häufig in Umfragen gemessen wird, von der Annahme ausgeht, dass sich Menschen normalerweise ein Maximum an Sicherheit wünschen. Empirische Ergebnisse legen aber mittlerweile nahe, dass dies nicht der Fall ist: Wenn Menschen Angst vor der Kriminalität zum Ausdruck bringen oder sich Sorgen über bestimmte Sicherheitsvorfälle machen, bedeutet dies nicht weder, dass sie zusätzliche Sicherheitsmaßnahmen unterstützen, noch dass die Menschen das Gefühl haben, deswegen ihre Grundrechte und Freiheiten aufgeben zu müssen.
Vielmehr scheint es darauf anzukommen, in welchem Maße die Bürger den öffentlichen und privaten Sicherheitskräften vertrauen. Der momentane Widerstand gegen Massenüberwachung durch die Geheimdienste legt jedenfalls nahe, dass es bei einem Teil der europäischen Öffentlichkeit zu einem erheblichen Vertrauensverlust gegenüber staatlichen Institutionen gekommen ist. Die in Kürze vorliegenden Ergebnisse der Umfrage sollte eine genauere Beantwortung dieser Frage ermöglichen und entsprechende Vorschläge für die Politik untermauern.
Alle PRISMS Forschungsberichte sind auf der Projekt-Webseite (http://prismsproject.eu) verfügbar.

Final EVITA Workshop on Security of Automotive On-Board Networks
23 November 2011, Honda Academy in Erlensee, Germany
In order to present major results of the project to the public, the EVITA consortium held a Workshop on Security of Automotive On-Board Networks. The workshop took place before the Car 2 Car Forum 2011 at the Honda Academy in Erlensee (near Frankfurt/Main, Germany). After presenting the main points of the specifications of the security building blocks, the consortium showed desktop and vehicle demonstrators for various automotive applications that require security measures.

EVITA E-safety vehicle intrusion protected applications
Background & Objectives
Future automotive safety applications based on vehicle-to-vehicle and vehicle-to-infrastructure communication have been identified as a means for decreasing the number of fatal traffic accidents. Examples of such applications are local danger warnings and electronic emergency brakes. While these functionalities inspire a new era of traffic safety, new security requirements need to be considered in order to prevent attacks on these systems. Examples of such threats are forced malfunctioning of safety-critical components or the interference with the traffic flow by means of fake messages.
Secure and trustworthy intra-vehicular communication is the basis for trustworthy communication among cars or between cars and the infrastructure. Therefore, the objective of the EVITA project is to design, verify, and prototype an architecture for automotive on-board networks where security-relevant components are protected against tampering and sensitive data are protected against compromise when transferred inside a vehicle.
By focusing on the protection of the intra-vehicle communication EVITA complements other e-safety related projects that focus on the protection of the vehicle-to-X communication.
Work Plan
Security requirements analysis
Starting from relevant use cases and security threat scenarios, security requirements for on-board networks will be specified. Also legal requirements on privacy, data protection, and liability issues will be considered.
Secure on-board architecture design
Based on the security requirements and the automotive constraints, a secure on-board architecture and secure on-board communications protocols will be designed. The security functions will be partitioned between software and hardware. The root of trust will be placed in hardware security modules that may be realised as extensions to automotive controllers or as dedicated security controller chips.
In order to ensure that the identified requirements are satisfied, selected parts of the secure on-board architecture and the communications protocols will be modelled using UML and automata and verified using a set of different but complementary model-based verification tools.
Implementation
For prototyping, FPGA’s will be used to extend standard automotive controllers with the functionality of cryptographic coprocessors. The low-level drivers for interacting with the hardware will be partially generated from UML models.
For even faster prototyping, the security functionality will also be implemented purely in software. An API will be defined so that applications on top of this API can use the cryptographic functions regardless of whether they are provided in hardware or software. All developed code will be validated to ensure its correctness.
Prototype-based demonstration
The secure on-board communication will be deployed inside a lab car demonstrating e-safety applications based on vehicle-to-X communication. Cryptographic methods will ensure the integrity and authenticity of information exchanged within the vehicle and will protect the electronic control units against theft, tampering, and unauthorised cloning.
Releasing the automotive hardware security modules for deployment in cars on public roads requires further implementation and testing efforts, which are out of scope of this project.
Dissemination and external interfaces
In order that the entire automotive industry may benefit from the project results, the secure on-board architecture and communications protocol specifications will be published as open specifications.
The EVITA project partners will liaise with related initiatives in the fields of e-safety and embedded security to achieve multilateral synergies.
Project duration
July 2008 – December 2011
Project Partners
Deliverables
Public reports
SysML models
Requirement diagrams for automotive on-board networks
These models are to be viewed with the open source UML toolkit TTool.
Publications
2011
- M. Wolf, T. Gendrullis: Design, implementation, and evaluation of a vehicular hardware security module. In 14th International Conference on Information Security and Cryptology, Seoul, South Korea, November/December 2011 – Paper
- H. Schweppe, B. Weyl, Y. Roudier, M.S. Idrees, T. Gendrullis, M. Wolf: Securing car2X applications with effective hardware-software co-design for vehicular on-board networks. In 27th Joint VDI/VW Automotive Security Conference, Berlin, Germany, October 2011. VDI Berichte 2131 – Paper
- G. Pedroza, M.S. Idrees, L. Apvrille, Y. Roudier: A formal methodology applied to secure over-the-air automotive applications. In 74th IEEE Vehicular Technology Conference (VTC2011-Fall), San Francisco, CA, USA, September 2011 – Paper
- H. Schweppe, Y. Roudier, B. Weyl, L. Apvrille, D. Scheuermann: Car2X communication – Securing the last meter. In 4th International Symposium on Wireless Vehicular Communications (WIVEC 2011), San Francisco, CA, USA, September 2011 – Paper
- G. Pedroza, L. Apvrille, D. Knorreck: AVATAR: A SysML environment for the formal verification of safety and security properties. In 11th International Conference on New Technologies of Distributed Systems (NOTERE), Paris, France, May 2011 – Paper
- M.S. Idrees, H. Schweppe, Y. Roudier, M. Wolf, D. Scheuermann, and O. Henniger: Secure automotive on-board protocols: A case of over-the-air firmware updates. In T. Strang, A. Festag, A. Vinel, R. Mehmood, C. Rico Garcia und M. Röckl, eds., 3rd International Nets4Cars/Nets4Trains Workshop, Oberpfaffenhofen, Germany, March 2011. Springer (LNCS vol. 6596) – Paper
- A. Fuchs, S. Gürgens, and C. Rudolph: A formal notion of trust and confidentiality – Enabling reasoning about system security. In Journal of Information Processing, vol. 19 (2011), pp. 274–291 –Paper
2010
- O. Henniger: Secure automotive on-board networks – Basis for secure vehicle-to-X communication. In Workshop “Staufrei von Holland nach Hessen” (From Holland to Hesse without traffic jam), Frankfurt/Main, Germany, December 2010 – Slides
- G. Pedroza, L. Apvrille, and R. Pacalet: A formal security model for verification of automotive embedded applications. In 3rd Sophia-Antipolis Formal Analysis Workshop (SAFA 2010), Sophia-Antipolis, France, October 2010 – Paper
- D. Knorreck, L. Apvrille, and R. Pacalet: Partitioning of in-vehicle systems-on-chip: a methodology based on DIPLODOCUS. In 13th Sophia-Antipolis Microelectronics Forum (SAME 2010), Sophia-Antipolis, France, October 2010 – Paper
- L. Apvrille, R. El Khayari, O. Henniger, Y. Roudier, H. Schweppe, H. Seudié, B. Weyl, M. Wolf: Secure automotive on-board electronics network architecture. In FISITA 2010 World Automotive Congress, Budapest, Hungary, May/June 2010 – Paper
- M.S. Idrees, Y. Roudier, and L. Apvrille: A framework towards the efficient identification and modelling of security requirements. In 5th Conference on Security in Network Architectures and Information Systems (SAR-SSI 2010), Menton, France, May 2010
- H. Schweppe, Y. Roudier: Security issues in vehicular systems: Threats, emerging solutions and standards. In 5th Conference on Security in Network Architectures and Information Systems (SAR-SSI 2010), Menton, France, May 2010 – Paper
- A. Ruddle: Security risk analysis approach for on-board vehicle networks. In “The Fully Networked Car” Workshop at the Geneva International Motor Show, Geneva, Switzerland, March 2010 – Slides
2009
- O. Henniger and H. Seudié: EVITA-project.org: E-safety vehicle intrusion protected applications. In 7thescar (Embedded Security in Cars) Conference, Düsseldorf, Germany, November 2009, invited talk –Slides
- H. Seudié: Vehicular on-board security: EVITA project. In C2C-CC Liaison Security Workshop, Wolfsburg, Germany, November 2009, invited talk – Slides
- O. Henniger, L. Apvrille, A. Fuchs, Y. Roudier, A. Ruddle, and B. Weyl: Security requirements for automotive on-board networks. In 9th International Conference on Intelligent Transport System Telecommunications (ITST 2009), Lille, France, October 2009 – Paper
- B. Weyl, O. Henniger, A. Ruddle, H. Seudié, M. Wolf, and T. Wollinger: Securing vehicular on-board IT systems: The EVITA Project. In 25th Joint VDI/VW Automotive Security Conference, Ingolstadt, Germany, October 2009 – Paper
- F. Stumpf, B. Weyl, C. Meves, M. Wolf: A security architecture for multipurpose ECUs in vehicles. In 25th Joint VDI/VW Automotive Security Conference, Ingolstadt, Germany, October 2009 – Paper
- T. Kosch: Privacy and data protection for drivers – A contribution from the EVITA project. In 16th ITS World Congress, Stockholm, Sweden, September 2009, invited talk – Slides
- M. Wolf: Designing secure automotive hardware for enhancing traffic safety. In CAST Workshop “Mobile Security for Intelligent Cars”, Darmstadt, Germany, August 2009, invited talk – Slides
- A. Fuchs and R. Rieke: Identification of authenticity requirements in systems of systems by functional security analysis. In Workshop on Architecting Dependable Systems at the IEEE/IFIP International Conference on Dependable Systems and Networks (DSN-2009), Estoril, Portugal, June 2009 – Paper
2008
- M. Wolf: Vehicular security hardware. In 6th escar (Embedded Security in Cars) Conference, Hamburg, Germany, November 2008, invited talk – Slides

E-safety Vehicle Intrusion proTected Application (EVITA)
Car to car and car to infrastructure communication has a great potential to further decrease road fatalities. But this implies a massive deployment of a communication infrastructure comprising the car, and consequently opens the door to vehicle intrusion threats, which will in turn create substantial threats to the overall car safety functions. Consequences may range from irritating malfunction of on-board commodity devices to dangerous failures, e.g. missing support for braking and/or steering which can create life threatening situations.It is the distinct objective of EVITA to address these threats by preventing unauthorised manipulation of on-board systems in order to successfully prevent the intrusion into the in-vehicular systems and the transmission of corrupted data to the outside. By focusing on vehicle intrusion projection EVITA complements SeVeCOM and NoW which focus on communication protection.Starting from identifying the necessary industrial use cases regarding assembly and field maintenance and compiling profound scenarios of possible threats, the overall security requirements are defined. On this basis a secure trust model will be compiled and a secure on-board architecture and protocol will be specified, verified, validated and, lastly, demonstrated. EVITA will release the architecture and protocol specification as an open standard.The consortium brings together all relevant expertise to successfully take the challenge: a car manufacturer, tier-one suppliers, security, hardware, software and legal experts. In order to guarantee a broad uptake of the open standard, EVITA will cooperate with the Car 2 Car Communication Consortium.
Status
Finished (07/2008-12/2011)
Clients
7th Framework Programme, European Commission, DG Information Society, Unit G4
Partners
- Fraunhofer Institute for Secure Information Technology (SIT), DE
- Robert Bosch GmbH, DE
- Continental Teves AG & Co. oHG, DE
- ESCRYPT GmbH, DE
- Infineon, DE
- Fujitsu Services AB, SE
- MIRA Ltd, UK
- Trialog, FR
- KU Leuven, BE
- BMW Forschung und Technik GmbH, DE
- GROUPE DES ECOLES DES TELECOMMUNICATIONS (institut Telecom), FR
- INSTITUT EURECOM, FR
Website
Deliverables with ISI contributions
- Dumortier, Jos, Christophe Geuens, Alastair Ruddle, Lester Low, and Michael Friedewald, “Legal framework and requirements of automotive on-board networks”, EVITA Deliverable 2.4, EVITA Project, 2011. http://www.evita-project.org/Deliverables/EVITAD2.4.pdf
- Ruddle, Alastair, David Ward, Benjamin Weyl, Sabir Idrees, Yves Roudier, Michael Friedewald, Timo Leimbach, Andreas Fuchs, Sigrid Gürgens, Olaf Henniger, Roland Rieke, Matthias Ritscher, Henrik Broberg, Ludovic Apvrille, Renaud Pacalet, and Gabriel Pedroza, “Security requirements for automotive on-board networks based on dark-side scenarios”, EVITA Deliverable 2.3, 2009. http://www.evita-project.org/Deliverables/EVITAD2.3.pdf
- Kelling, Enno, Michael Friedewald, Timo Leimbach, Marc Menzel, Peter Säger, Hervé Seudié, and Benjamin Weyl, “E-safety vehicle intrusion protected applications: Specification and Evaluation of e-Security relevant use cases “, EVITA Deliverable 2.1, 2009. http://www.evita-project.org/Deliverables/EVITAD2.1.pdf
EVITA at escar Conference

9-10 November 2011, Dresden, Germany
EVITA demonstrators and a project summary are presented at the 9thescar (Embedded Security in Cars) Conference in Dresden, Germany. The escar conference counts as a leading conference on IT security in vehicles.

Final EVITA Workshop on Security of Automotive On-Board Networks

23 November 2011, Honda Academy in Erlensee, Germany
In order to present major results of the project to the public, the EVITA consortium holds a Workshop on Security of Automotive On-Board Networks. The workshop takes place before the Car 2 Car Forum 2011 at the Honda Academy in Erlensee (near Frankfurt/Main, Germany). After presenting the main points of the specifications of the security building blocks, the consortium shows desktop and vehicle demonstrators for various automotive applications that require security measures.